Encrypting Internet traffic sounds great, but how exactly do you do it? And what are the advantages of taking care of this in the first place?
Well here is an in depth and easy to understand article on how to encrypt internet connections. Don’t worry, it’s a quick read, nine minutes tops.
What Exactly Is Encryption?
To keep things simple, encryption is the process of converting data from a readable format to an unreadable one. In essence, it is about using an encryption key to protect data. Only someone who has that key (or a specific decryption key) can read it.
“Unreadable formatting” is pretty vague, but you can use this tool to get an idea of what it would look like.
In our case, we use AES-256 encryption to encrypt this “Hey guys!” message. This is the encryption key we use “fgj5kig0813sfdfewbasd3453gafvafg”. Encrypted, the message looks like this: “bTFR + qKhkQt2djukrfX + Zw ==”.
Anyone trying to monitor the content of that message will only see that encrypted output. Only someone who has the original encryption key or a different decryption key can decrypt the message to see the “Hey guys!” text.
Can Encryption Be Broken?
If you use an outdated cipher cipher (such as Blowfish) with a small key size (64 bits, for example), a brute force attack can crack it.
But if you stick to modern ciphers like AES and large key sizes (128 bits and up), you’re safe. If Tianhe-2, the world’s fourth-fastest supercomputer , tried to crack an AES-256-encrypted message, it would take about 9.63 × 1052 years (1052 in this case is a 1 with 52 zeros, multiplied by 9)
Of course, as supercomputers become more and more advanced in the future, they will be able to crack modern ciphers faster. But at the same time, the encryption ciphers will also be more advanced, so they will cancel each other out.
Why do you need to encrypt your Internet connection?
Is there any point in bothering to do this?
Yes. In fact, there are many reasons to make your Internet traffic unreadable:
- First of all, hackers can eavesdrop on and intercept unencrypted connections. They can steal sensitive information that way (credit card details, passwords, etc.) or redirect you to phishing websites (since they see what URL you’ll go to).
- Cybercriminals can trick your device into connecting to a fake WiFi networkthat they control. If that happens, they can monitor all of your online communications.
- Unencrypted traffic means your ISP can analyze your data packets to see what websites you browse and what web applications you use. With that information, they can limit your bandwidth .
- If you use unencrypted connections, that means you’re okay with your ISP selling your browsing data to advertisers .
- Not encrypting your traffic means network administrators can monitor it. That can be a problem if you’re caught accessing “distracting” websites at work or school, like YouTube, Facebook, or Twitter.
- Stop governments from spying on everything you do online.
“But I’m already using encrypted WiFi, so I’m fine, right?”
Not at all. When you Google how to encrypt Internet connections, many articles will tell you to use encrypted networks (basically ones that require a password to access).
Well, here’s the rub: Most networks use WPA2 for encryption. Unfortunately, that security standard is not very good and has serious vulnerabilities . Actually, you can find many tutorials online that show you different ways to crack WPA2 passwords ( here , here , and here ).
The new WPA3 encryption standard is supposed to fix those problems, but even it’s not without its flaws .
Also, here’s another problem: some networks may require a password to use them, but may use outdated encryption like WEP and WPA.
In general, just because you use encrypted WiFi doesn’t mean your data is safe.
How to Encrypt Internet Connections.
Based on our research, you have six options at your disposal. You don’t have to use all of them, but if you really want to make sure none of your traffic is exposed, it’s best to try them all together:
1. Only Browse HTTPS Websites
HTTPS is the standard today, and some browsers won’t even let you connect to an HTTP website, and for good reason! HTTP means that the website does not encrypt your connection requests and responses. So anyone can spy on them.
It’s okay if you just use an HTTP website to review memes. But if you use it to make payments or enter personal information, you will have a hard time since anyone can see that data.
Therefore, if you really want to learn how to encrypt Internet connections, we recommend that you avoid HTTP websites. Only browse HTTPS sites as they automatically encrypt your traffic when you visit them.
2. Use HTTPS Everywhere
HTTPS Everywhere is a browser extension for Opera, Chrome, Firefox, Tor and Brave that automatically redirects all HTTP links to HTTPS pages if available. It’s quite useful as some big websites still don’t use HTTPS .
Of course, HTTPS Everywhere won’t really help you if the site just doesn’t support HTTPS. But it’s still a good security measure.
Lastly, consider using uMatrix and uBlock Origin as well. They do not encrypt your connection, but they can block malicious scripts and ads. That really comes in handy if you somehow land on a suspicious HTTP website.
3. Use Only End-to-End Encrypted Messaging Apps
Whenever you want to send someone a message, just type a text on your smartphone and send it, right? Or send them a message through Facebook Messenger.
Those methods are convenient, sure, but they’re not really private. Text messages can be exposed or leaked if the company that handles them does not use any encryption to protect them. Also, Facebook Messenger doesn’t use end-to-end encryption by default, which means the company can monitor your conversations with your friends .
And that’s not all. Consider the fact that the NSA is known to collect millions of text messages , and that companies like Apple, Facebook, and Skype are part of its surveillance program (PRISM).
Sure, you can use end-to-end encryption with Facebook Messenger if you enable the Secret Conversation feature . But here’s the rub: It won’t encrypt group messages, GIFs, payments, or voice and video calls. And again: Facebook is part of the NSA’s surveillance program. How much can you trust your encryption?
If you really want to secure your connections, you need an app that doesn’t raise any red flags. Here are some recommendations:
- Signal: The app has been recommended by privacy advocates like Edward Snowden and Bruce Schneider, and is even the app of choice for the European Commission . In addition to having end-to-end encryption, it is also open source. Although he recently had a spying situation , the problem was quickly fixed.
- Wickr– While it’s primarily aimed at businesses, people can use it too. It’s open, end-to-end encrypted, and doesn’t require an email address or phone number to sign up.
- LINE– A very secure app that started as a communication solution developed by Japanese engineers after an earthquake in 2011.
- Threema: Although not free, it offers excellent security: end-to-end encryption, no phone numbers required, and it removes your messages from servers once they’ve been delivered.
Let’s take a look at an encrypted messaging app that almost everyone recommends:
- WhatsApp: While it offers end-to-end encryption and Facebook confirmed that they can’t read WhatsApp messages, there is still the PRISM problem, that is, Facebook is part of it. That means they share data with the NSA. Also, the app had issues with spyware in 2019 .
We are not saying that you should not use WhatsApp at all. But if you do, be careful what you share on it.
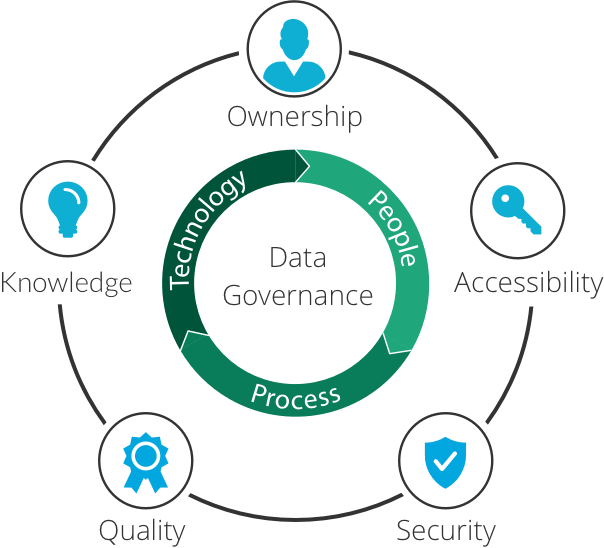
4. Use DNS Over HTTPS
DNS stands for Domain Name System, and its function is to translate IP addresses into website names and vice versa.
When you want to connect to a website by name, your browser will send a DNS query to your ISP’s DNS server to retrieve the IP address of the site.
So far so good, but here’s the rub: DNS queries are generally not encrypted. That exposes you to many risks: MITM (Man In The Middle) attacks, ISPs spying on your browsing, and DNS filtering.
And that is exactly the problem that DNS solves. It uses HTTPS to encrypt your queries, which makes your Internet connection more private.
However, how do you use DNS over HTTPS?
It’s not too difficult since most browsers already support it. Here is a guide showing you how to enable it. If you want to use DNS over HTTPS outside of your browser, try 1.1.1.1 (tutorials included on the site). It is much faster than OpenDNS or Google Public DNS.
5. Use a VPN
A VPN is one of the easiest ways to fully encrypt your internet connection. It is an online service that hides your IP address and encrypts all your web traffic. Is that how it works:
- Use a VPN client on your device to connect to a VPN server .
- The client and server negotiate the connection and establish an encrypted tunnel between them.
- From then on, all your traffic will go through that tunnel. If someone tries to monitor you, you’ll only see gibberish (like the encrypted message example we gave you at the beginning).
VPNs are very simple to use, and most of them use the latest encryption. You can read more about VPN encryption in our guide .
Start encrypting your Internet connections with CactusVPN right away!
If you need a VPN, just check out our service . We offer AES-256 encryption for most protocols, which is basically military-grade security. On top of that, we don’t keep any logs, we offer secure protocols like IKEv2, SoftEther, and OpenVPN, and we have support for DNS over HTTPS.
6. Use Encrypted Email Services
Gmail, AOL and Yahoo! They may be popular and convenient, but they’re not a good way to encrypt all the email data that passes through your Internet connection. Here’s why:
- Google allows third parties to analyze your emails . Yahoo! and AOL have also been accused of scanning emails for data they can sell to advertisers .
- About three billion Yahoo! were exposed to a data breach.
- AOL reportedly has the highest email breach rate .
- Despite making promises, Yahoo! and Google haven’t implemented end-to-end encryption yet, which means they can scan your emails on your end. Many other email providers on the market had no problem offering it, so this is a pretty big red flag.
You’re much better off with a service like ProtonMail or Tutanota . Both are open source, offer end-to-end encryption, and do not require or store any personal information.
Should You Encrypt Your Connections With Tor?
Many articles and people will tell you to do this. It’s mainly because Tor adds multiple layers of encryption to your connections (usually three).
Although that sounds good, there are some problems:
- The exit node (the last Tor server your traffic passes through) decrypts your data. So you can see the content of your traffic . If a cybercriminal or government agent were to run the node, they could spy on your Internet connections.
- Wait: hackers and government agents? Running my Tor nodes? It is more common than you think. Researchers have managed to find malicious nodes before , and it’s not exactly a secret that law enforcement can actually run some nodes .
- Tor has some suspicious ties to the US government. He can read more about them here (points 5 and 6).
If you really want to encrypt your internet connection with Tor, you have to run it through a VPN. By that, we mean that you need to connect to a VPN server before connecting to the Tor network. That way, even if a malicious node decrypts your Tor traffic, the person running it will only see encrypted VPN traffic.
However, keep in mind that if you do that, you’ll get pretty lousy speeds. Tor already has slow speeds, and a VPN slows them down too .
Remember To Use Antivirus Software Too!
Encryption is a great way to protect your data from hackers, but it can’t protect your device from malwareinfections . All the solutions mentioned in this article will only protect your data at the online level, not offline or hardware.
So make sure to use antivirus solutions on all devices.
How to Encrypt Internet Connections: The Bottom Line
Encrypting your web traffic is very important if you want to prevent cyberattacks, widespread ISP snooping, and government surveillance.
The best way to encrypt your connections is to use encrypted messaging apps, VPNs , encrypted email services, DNS over HTTPS, HTTPS websites, and HTTPS everywhere.